Author: Onkar Singh, CoinTelegraph; Compiled by: Deng Tong, Bitchain Vision
1. What is the teardrop attack in cryptocurrency?
Tears attacks exploit the way the system reorganizes fragmented packets by sending overlapping fragments during transmission, which the target system fails to rebuild correctly, resulting in a denial of service.
As the cryptocurrency ecosystem matures, cyber threats to attack the cryptocurrency ecosystem have become increasingly complex.A teardrop attack is a denial of service (DoS) attack, which is one of such cyber attacks.Tears attacks were initially a network-level vulnerability, and their adaptation to cryptocurrency systems underlined the originality and versatility of malicious actors.
Imagine cutting a letter into several parts and placing it in different envelopes.Someone re-patched the pieces at the destination to read the entire letter.Tears attacks are like sending missing or overlapping envelopes, which makes it impossible to recreate the original letter.Due to this confusion, the receiver may be overwhelmed and shut down.
But what does this have to do with cryptocurrencies?
Cryptocurrency systems rely heavily on network communications.Transactions, block propagation and other basic functions involve sending data in packet form over the Internet.These packets are reassembled by nodes that maintain the blockchain and process transactions.
Tears attacks targeting specific nodes or network participants attempt to interfere with conventional operations to exploit weaknesses in wallets, exchanges, or blockchain networks.For example, by sending malformed packets, an attacker can overwhelm the server’s reorganization process, causing it to crash or be unresponsive.
If the teardrop attack works, it may open the door for other attacks.For example, when the server is unavailable or cannot reassemble a packet, an attacker may attempt to exploit other weaknesses to obtain unauthorized access or change the data.
Therefore, it is crucial to understand and address the consequences of such attacks, as they have the potential to undermine the integrity of the blockchain network.
2. How to target encrypted networks with teardrop attacks
In cryptocurrency environments, teardrop attacks often target the decentralized nature of blockchain platforms.Even if they don’t target blockchain’s crypto algorithms, destroying the underlying peer-to-peer network infrastructure on which cryptocurrencies rely can lead to service disruptions, loss of funds and a decline in user trust.
An attacker can interfere with consensus processes, transaction verification, or node-to-node communication by focusing on a specific node or server.This can lead to network fragmentation, processing delays, and even completely shutdown.
For example, an attacker may overwhelm key nodes in a permissionless blockchain (such as Bitcoin) or verification nodes in a permissioned blockchain with a wrong packet, making it unable to run.Because nodes rely on regular communication to reach consensus, these interruptions can lead to vulnerabilities that allow attackers to exploit network exceptions.
For example, if some nodes are temporarily disconnected or cannot run, an attacker may attempt to manipulate the data flow, trigger a double payment attack, or introduce a wrong transaction.
Furthermore, teardrop attacks can target services related to the blockchain ecosystem, such as wallet providers and cryptocurrency exchanges, rather than the blockchain infrastructure itself.These services rely primarily on continuous communication between users and servers for seamless transactions and service availability.
The exchange’s teardrop attack could disrupt transactions, withdrawals and other critical services.In addition to negatively affecting specific users, this can also damage the reputation of the exchange and can cause losses to traders and investors.In addition, frequent attacks or prolonged disruptions may cause users to lose confidence in the platform, thereby damaging their user base.
3. The impact of teardrop attack on encryption security and users
Tears attacks have a profound impact on cryptocurrency systems.In addition to jeopardizing network security, they also undermine user trust.
The main impacts include:
-
Operation downtime:Network participants (such as nodes or verification entities) may experience interruptions, thereby stopping transaction processing.
-
Financial loss:Traders and investors may suffer financial losses due to delays or failures in transactions, especially during periods of market volatility.
-
Data Integrity Risk:While teardrop attacks do not directly modify blockchain data, they may create opportunities for secondary attacks on ledger integrity.
-
Reputation damage:Cryptocurrency networks, exchanges or wallet providers may suffer prolonged interruptions or repeated attacks.
-
Utilize window:An attacker can use network outages to distract system administrators from further attacks, such as phishing or double payments.
4. How to identify teardrop attacks
To minimize the harm caused by teardrop attacks, early identification is required.If system administrators are aware of the signs of risk, they can act faster.
Here are the main signs of teardrop attack:
-
Unexplained system crash:Frequent crashes may indicate that the system is under attack, and its target is the ability to reorganize fragmented packets.
-
Performance degradation:A slower processing time or a reduced responsiveness of a node or server can indicate a large influx of malformed data packets, causing the system to be overwhelmed.
-
Error log:A careful examination of the system log may reveal overlapping or incomplete packet patterns, which are typical of teardrop attacks.
-
Abnormal network traffic:A sudden surge in fragmented packet traffic usually indicates a teardrop attack.Anomaly trends can be discovered with the help of monitoring tools.
-
Connection issues:If nodes in the network cannot communicate with each other, it may be a sign that the blockchain architecture is under attack.
5. Best practices to prevent teardrop attacks in encryption
An active strategy that combines operational concerns and technical assurance is needed to prevent teardrop attacks.
Packet filtering is often used in traditional networks to prevent sabotage such as DoS attacks, which are designed to overload the network with malicious data.
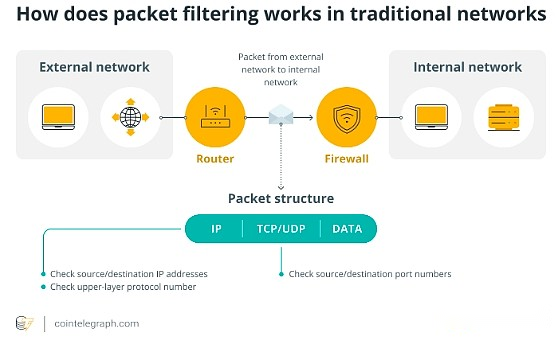
Simply put, packet filtering acts as a security checkpoint for data transmission over the network.Just like airport security personnel scan your luggage for dangerous items, packet filtering scans incoming packets to ensure they are safe.
In blockchain systems, it helps prevent malicious or faulty packets, such as those used for teardrop attacks, from entering network nodes.
Here are some other best practices to consider:
-
Decentralized architecture elasticity:Strengthen decentralized blockchain nodes to ensure redundancy and fallback mechanisms, and maintain the normal operation of the network even if some nodes are attacked.
-
Rate limiting and flow shaping:Controls the rate at which packets are transmitted to the nodes to reduce the impact of flood attacks.
-
Regular software updates:Ensure that all blockchain software, wallets and trading platforms have been updated to patch known vulnerabilities.
-
Education and training staff:Give teams knowledge to effectively identify and mitigate potential threats.
Combined with other defense technologies, packet filtering provides a powerful layer of protection that helps ensure cryptocurrency systems are protected from evolving threats.
6. What to do if you become a victim of cryptocurrency teardrop attacks
Even with the strongest defense measures, no system can fully resist cyberattacks.Taking action in time may mitigate the impact of teardrop attacks on your cryptocurrency system.
If you are a victim of a teardrop attack, you can do the following:
-
Isolate affected systems:To prevent the attack from spreading, disconnect the hacked node from the network.
-
Analysis and mitigation:Companies can use forensic tools and detailed logs to investigate the nature of the attack.To resolve exploited vulnerabilities, apply the necessary updates or fixes.
-
Hire an incident response team:Utilize the knowledge of cybersecurity experts to help contain and recover.
-
Notify stakeholders:Explain the issue clearly to consumers and relevant parties.Regular updates and transparency help maintain trust.
-
Enhanced defense capabilities:Assess the system’s security architecture after an attack and take precautions to prevent recurrence.To find more vulnerabilities, perform penetration testing (simulate attacks to identify weaknesses).
-
Record events:Record detailed records of attacks and responses.This knowledge can be very helpful for future compliance and preparation.
This shows that teardrop attacks highlight the vulnerability of cryptocurrency systems in the face of complex cyber threats.By taking action quickly and strengthening security measures, you can mitigate impact and protect your network from future disruptions.