Banking on the blockchain: issues facing the next twenty years
Banks rely on ledgers, and the most essential part of blockchain is also ledgers..But there is a fundamental difference between this ledger and that ledger.The choice faced by banks today…
Deconstructing how PeerDAS can help Ethereum regain “data sovereignty”
Written by: imToken At the end of 2025, the Ethereum community ushered in the conclusion of the Fusaka upgrade relatively calmly. Looking back on the past year, although discussions about…
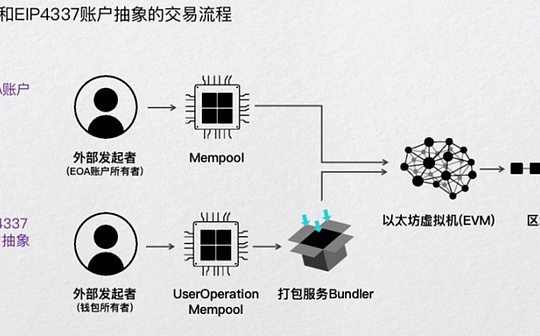
One article to understand how Account Abstraction (AA) reconstructs the Web3 experience
Written by: imToken Preface: In addition to mnemonics, how else can we manage assets? For a long time in the past, mnemonic words were not only the only key to…
v2 version of x402
Author:YQ,compile:Block unicorn The v2 version of the x402 protocol is based on production deployment experience and represents a fundamental architectural change (if you are interested, you can go to the…
Interpretation of Fusaka Upgrade: The Beginning of Ethereum’s “Data Hegemony”?
Author:K threeKai; Source: X,@kaikaibtc It has been 8 days since the Ethereum Fusaka (Fulu + Osaka) upgrade was officially activated. There were no price spikes and no network outages.It’s as…
Account abstract research report: ETH account system intergenerational transition and the pattern of the next five years
pickwant Ethereum will undergo a major upgrade called Fusaka on December 3, 2025. This is the third milestone update of Ethereum since the Merge and Dencun upgrade. It is designed…
The so-called “building L2 ecosystem” has been falsified
Author: Godot; Source: @GodotSancho Recently I have seen a lot of discussions about Monad $MON and public chain moats.As a contributor to L2, I really feelThe so-called “building an ecology”…
What is Brevis, who was appointed by the Ethereum Foundation, planning?
Author: Haotian; Source: X, @tmel0211 On eth_proofs Day, Justin Drake used the zklighthouse client to verify Brevis Pico ZKVM’s proof on-site – it can directly finalize blocks without re-executing transactions,…
Zero-knowledge proofs: How transformative can they be?
Author:0xKira Preface In the ever-evolving landscape of cryptography and blockchain, few innovations have attracted as much attention as zero-knowledge (ZK) proofs.Once an obscure academic concept in computer science theoretical papers,…
Interpret the real reason why Bitcoin Core v30 relaxed the OP_RETURN restriction
Author: Aaron Zhang; Source: X, @zzmjxy Bitcoin Core v30 relaxes the OP_RETURN restriction. Everyone is saying that it is because “Ordinals inscription restriction is invalid”. Over the past three months,…