Source: Economist; Translated by: AIMan@Bitchain Vision
Ben Zhou, owner of Dubai cryptocurrency exchange Bybit, recalled that February 21 was originally a normal day.Before going to bed, he approved the transfer of funds between company accounts, a “typical operation” performed when serving more than 60 million users around the world.Half an hour later, he received a call.”Ben, something went wrong,” his CFO said in a trembling voice.”We may have been hacked…all Ethereum has disappeared.”
Independent investigators and the U.S. FBI quickly pointed the finger at a familiar culprit: North Korea.Hackers from this hermit kingdom have become one of the biggest threats to the crypto industry and a significant source of income for the North Korean regime, helping it withstand international sanctions, controlling elites, and funding its missile and nuclear weapons programs.
According to data from cryptocurrency survey company Chainalysis, North Korean hackers stole a total of $661 million in 2023; in 2024, their theft amount doubled, stolen $1.34 billion in 47 thefts, equivalent to more than 60% of the total stolen cryptocurrency worldwide.
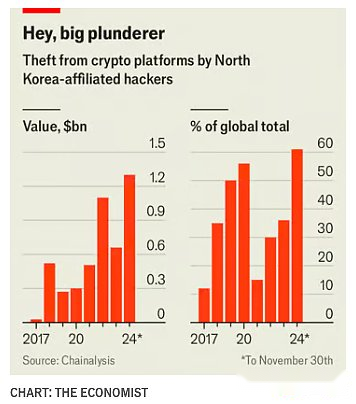
The ByBit stolen case shows that hackers’ technology and ambitions are growing: In a hacking attack, North Korea stole $1.5 billion from the exchange, the largest theft in cryptocurrency history.
Origin of North Korean cyber forces
North Korea’s attacks are the result of decades of efforts.The country’s first computer science school dates back to at least the 1980s.The Gulf War helped the regime recognize the importance of cyber technology to modern warfare.2Thae Yong Ho, a senior North Korean diplomat who defected in 2016, said talented math students were sent to special schools and were exempt from annual rural voluntary labor.North Korea’s cyber forces were initially conceived as espionage and sabotage tools, but began to focus on cybercrime in the mid-2010s.It is said that Kim Jong-un calls cyber warfare the “universal sword”.
Encryption attacks and money laundering
Theft of cryptocurrency involves two main stages.The first phase is invading the target system—which is equivalent to finding an underground passage to the bank’s vault.Phishing emails can insert malicious code.North Korean agents pretend to be recruiters, inducing software developers to open infected files in fake job interviews.Another approach is to use fake identities to get remote IT work at a foreign company, which may be the first step to accessing an account.”They are very good at finding vulnerabilities through social engineering,” said Andrew Fierman of Chainalysis. In the ByBit case, hackers hacked the computers of developers working for digital wallet software providers.
Once stolen, cryptocurrencies must be whitewashed.Black money is spread across multiple digital wallets, mixed with clean funds and transferred between different cryptocurrencies, a process known in the industry as “mixed coins” and “jump chains”.”They are the most experienced cryptocurrency money launderers we have ever encountered,” said Tom Robinson of Elliptic, a blockchain analytics firm. In the end, the stolen funds require withdrawal.
More and more underground services can help achieve this, many of which are related to organized crime.Law enforcement interceptions and obstacles reduce overall revenue, but Nick Carlsen, a former FBI analyst and now working for blockchain intelligence firm TRM Labs, saidNorth Korea expects to definitely get “80%, or even 90%” of its stolen funds.
Why is North Korea good at stealing cryptocurrencies
North Korea has several advantages.One is talent.This seems counterintuitive: the country is extremely poor and ordinary people cannot use the Internet or even computers.but“North Korea can select the best talents and tell them what to do”, said Kim Seung-joo of Seoul’s Korea University. “They don’t have to worry about them going to work at Samsung.”At the 2019 International College Programming Competition, a team from North Korea won eighth place, beating teams from Cambridge, Harvard, Oxford and Stanford.
These talents have also been utilized.North Korean hackers work day and night.They attacked with great courage.Jenny Jun of Georgia Tech said most state actors tried to avoid diplomatic rebound and “acted like they did in Eleven Arhats: wearing white gloves, quietly entered, stealing the crown stones, and leaving quietly.”North Korea does not “value confidentiality-they are not afraid of loud noises.”
What are the cryptocurrencies stolen by North Korea used for?
For the North Korean regime, stolen cryptocurrencies have become a lifeline, especially as international sanctions and the COVID-19 pandemic have curbed their already limited trade.Cryptocurrency theft is a more effective way to earn hard currency than traditional sources of hard currency, such as overseas labor or illegal drugs.The monitoring agency United Nations Expert Group (UNPE) reported in 2023 that cyber theft accounts for half of North Korea’s foreign exchange revenue.North Korea’s digital theft last year was more than three times its exports to China.”What millions of labor get, can be copied in just a few dozen people,” Mr. Carlson said.
These funds help support the North Korean regime.Hard currency is used to buy luxury goods to control the elite.It is also used to make weapons.It is believed that most of North Korea’s stolen cryptocurrency flows into its missile and nuclear weapons programs.
Will there be more North Korean hackers in the future
Cryptocurrency investigators are doing better and better at tracking stolen funds on blockchain.Mainstream cryptocurrency exchanges and stablecoin issuers often work with law enforcement to freeze stolen funds.In 2023, the United States, Japan and South Korea announced a joint operation aimed at combating North Korea’s cybercrime.The United States has imposed sanctions on several “coin-mixed” service providers used by North Korea.
However, the authorities are still one step behind.Hackers turned to other companies that offer similar services after the U.S. sanctions on North Korea’s favored coin mixers.Resolving this problem requires multilateral efforts from the government and the private sector, but this cooperation has been breaking down.Last year, Russia used its veto power at the United Nations to abolish the UN Cybersecurity Capacity Commission.President Donald Trump’s move to cut U.S. development aid hits plans aimed at building cybersecurity capabilities in fragile countries.
By comparison,North Korea is investing more and more resources in cybercrime.South Korean intelligence agencies estimate thatNorth Korea’s cybercrime team increased from 6,800 in 2022 to 8,400 last year.Abhishek Sharma of the Indian think tank Observer Research Foundation said that as the cryptocurrency industry expands in countries with weaker regulation, North Korea has an increasingly “rich target environment.”Mr Sharma noted that last year, North Korea attacked exchanges located in India and Indonesia.
As we all know, North Korea has already used AI in its operation.AI tools can help make phishing emails more convincing and easier to make at scale in multiple languages.They can also make it easier for remote IT workers to penetrate companies.Bad days like Mr. Zhou of Bybit may become more and more common.