Source: Beosin
On January 30, 2024, Beijing time, according to Beosin’s Eagleeye security risk monitoring, early warning and blocking platform monitoring display,The DEFI protocol MIM_SPELL was attacked by hackers Lightning loan, resulting in a loss of over 6 million US dollars.At present, the attacker will exchanges the stolen funds to ETH and transfer it to the two attackers’ addresses. Beosin Kyt will continue to monitor funds, and at the same time we analyze this vulnerability.
Vulnerability analysis
The main reason for this incident isThe attacker uses the project party contract to use the upward algorithm and control the parameter to 1. The maximum error control that will be taken up upward is used, which will lead to imbalances in the ledger.
There are two functions in the contract, which are BORROW and Repay, one is to borrow money from the contract, and the other is to pay the contract to the contract.
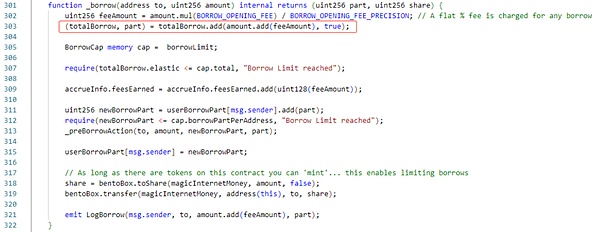
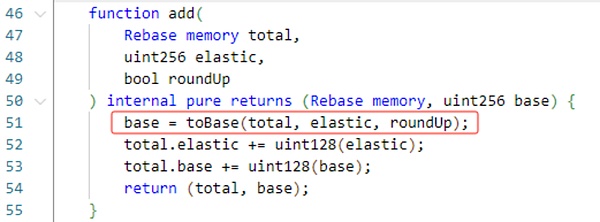
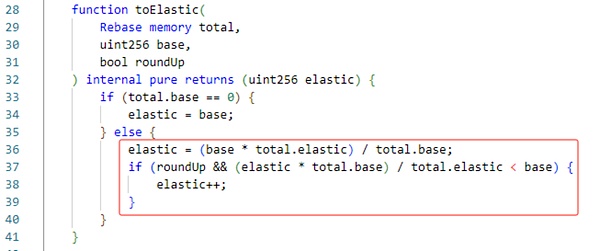
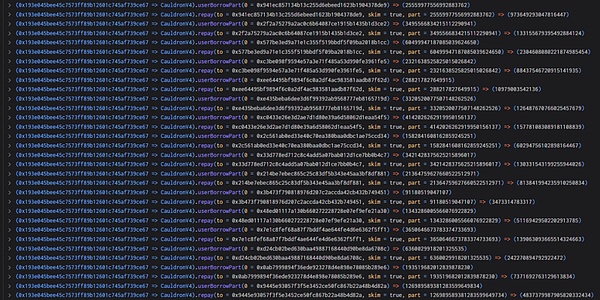
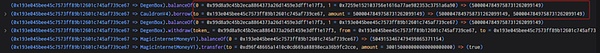
The BORROW function will specify the amount of borrowing, and the debt value is calculated by the proportional conversion, and the total debt value of the caller is updated.As shown in the figure below, the ADD algorithm of the contract here uses upwards.
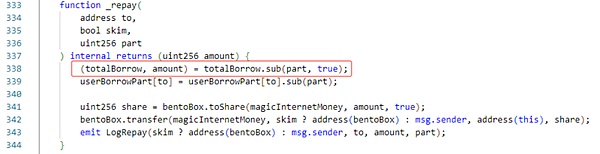
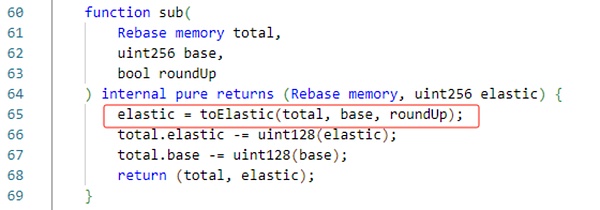
The BORROW function will specify the repayment debt value, and the amount of repayment is calculated by the proportional conversion, and the repayment amount is transferred to the contract.As shown in the figure below, the SUB algorithm of the contract here still uses upwards.
Understand the process of borrowing and repayment, let’s see how hackers use the vulnerability.
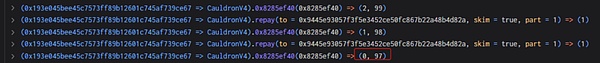
The hacker first controlled the amount and debt value of the contract to 0 and 97 (how to control will be introduced in the next section).
Next, the BORROW and REPAY functions are not stopped, and the borrowing and repayment values are 1. Finally, the amount of borrowing and debt value is controlled to 0 and 120080183818866665215049728, resulting in a serious imbalance.
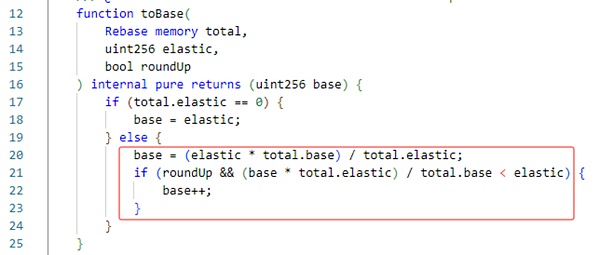
According to the above code rules (elastic = 0, base = 97), when the attacker calls the BORROW once and is passed in 1, the two ledger will become elastic = 1, base = 98 (elastic is 0, and will increase according to the value synchronization.), When calling again and being passed into 1 again, it will become elastic = 2, base = 196 (when Elastic is not 0, it will be added in proportion to).
Next, the attacker calls the repay function to pass 1, and call the SUB function. At this time, the calculated elastic should be equal to 1*1/196 = & gt;Elastic = 1, base = 195.It can be seen that at this time Elastic is unchanged, but the base doubles.
The attacker uses multiple above methods to bring Elastic = 0, Base = 1200801838106866665215049728.Eventually borrowed a contract with more than 5 million mIM through a BORROW.
Attack process
Understand the function of the function, let’s take a look at how the attacker performs the attack (one of the transactions as an example).
1. The attacker first borrowed 300,000 MIMs.
2. Subsequently, the attacker query the amount and debt value in the callback function. It can be seen that at this time it is 240,000 and 230,000.

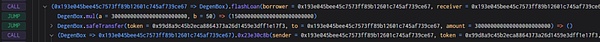
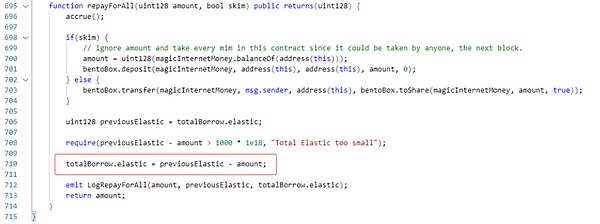
3. Next, the attacker calls the repayFrall function, returned 240,000 mIM tokens to control Elastic.

4. Next, the attacker returned the liabilities of other users through the REPAY function, and finally controlled the amount of loan and debt value to 0 and 97.
5. The attacker creates a new contract and controls the amount of borrowing and debt values to 0 and 12008018381886665215049728 by appealing BORROW and REPAY.
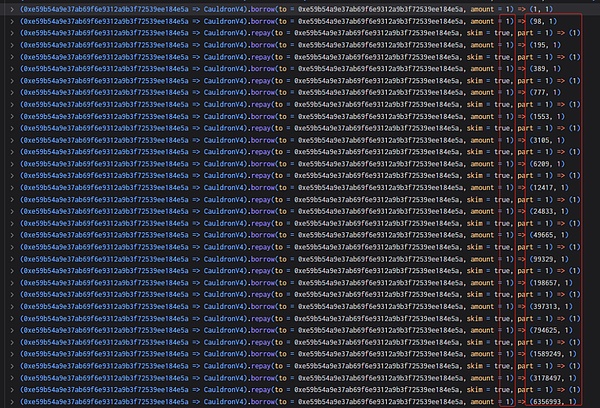
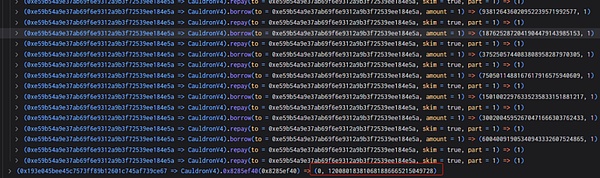
6. Finally, 5 million mIM borrowed 5 million mIM through a BORROW and repaid lightning loan.
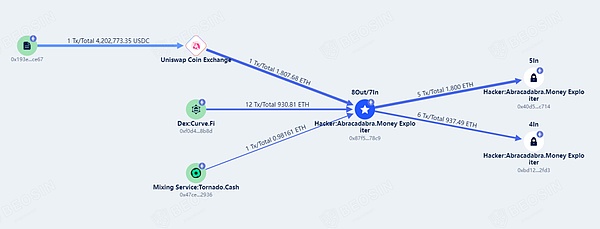
Fund tracking
As of press time, the stolen funds of over 6 million US dollars are exchanged for ETH, and the hacker address has not moved. The Beosin Kyt anti -money laundering platform will continue to monitor the funds.